What is Denial of Service Attacks and How to Prevent DDOS Attacks
Denial of Service Attacks
A denial of service attack (also known as DoS) is an attempt to make a device (computer or any other device attached to a network) unavailable by either completely shutting it down or making it slow, thus making the resource unavailable to the intended users. Sometimes a large number of computers are involved in an attack (forming a Botnet), that attack is known as Distributed Denial of Service (DDoS) Attacks.
Recent DoS attacks victims were some of the big names including Paypal, MasterCard, Visa, and the list goes on.
Although a DoS attack doesn’t generally breach the target organization’s security (in most cases, by causing a server overload), though it does cause heavy damage, by not being available to legitimate users. The consequences can be worse if the victim is a Bank or Payment Gateway.
Preventing DoS Attacks
There are various ways to protect your server from getting a Denial of Service attack, but for mitigating this kind of attack you should always keep your
- Softwares up to date
- Close any unused ports
- Implement security modules for your servers which are optional
- Keep redundant server, so that if one server goes down, still the other server can take the load
- Perform security audits, and check your log files for any attempt of flooding your server with request.
- Install security component mod_dosevasive if you are using apache.
There are major Security companies coming up with a unique filter, which filters the request and blocks the unwanted request and the IP of the originating address from where the request is coming.
Denial of Service attacks can be prevented by the use of a combination of attack detection, traffic classification, and response tools, which can block traffic from an attacker and allow traffic from a genuine user.
Firewalls prevent DOS by allowing or denying protocols, ports, or IP addresses. Switches also provide some rate-limiting and ACL features.
Some switches have automatic traffic shaping, delayed binding, deep packet inspection, and Bogon filtering to detect and prevent denial of service attacks through automatic rate filtering and WAN Link failover and balancing.
An example of this would be an SYN flood attack which can be prevented using delayed binding or TCP splicing. Similarly, content-based DoS can be prevented using deep packet inspection.
Similar to switches, routers have some manually configurable rate-limiting and ACL capability. If the attacks have signatures associated with them then Intrusion-prevention systems (IPS) are very useful. Intrusion-prevention systems which work on content recognition cannot block behavior-based DoS attacks which have legitimate content but bad intent.
DoS Defense System (DDS) can block connection-based DoS attacks and those with legitimate content but bad intent which was a drawback of an IPS. A DDOS is capable of addressing both protocol attacks (such as Teardrop and Ping of death) and rate-based attacks (such as ICMP floods and SYN floods)
But it is not possible to stop a DoS attack if an attacker manages to implant a Dos script inside your own server and starts DoS’ing your server. In this case, you have to carefully monitor your server content, check if any new files or scripts are added illegally inside your server.
Wireless and Web Pentesting
Course Description Network Penetration Testing course for beginners taking you from wondering what hackers do to set up a lab, learning Kali Linux, and…
Advance Ethical Hacking and Penetration Testing
Overview Ethical hacking is an extremely valuable job skill that the more applications, the more website, the more software that is created, the more…
Ethical Hacking and Penetration Testing
Overview Ethical hacking is an extremely valuable job skill that the more applications, the more website, the more software that is created, the more…
Advanced Python Scripting for Ethical Hackers
Many of the most powerful, memorable and effective photographs are black and white images. With digital photography though you can no longer take a…
Network Pentesting
Course Description @ Network Pentesting course for beginners taking you from wondering what hackers do to set up a lab, learning Kali Linux, and…
Proactive Cybersecurity for Individuals and Small Businesses
How You Can Protect Your Identity While Surfing Online, Starting Today…In This Step by Step Video Course While 99% of the population won’t do…
Python for Ethical Hackers
Many of the most powerful, memorable and effective photographs are black and white images. With digital photography though you can no longer take a…
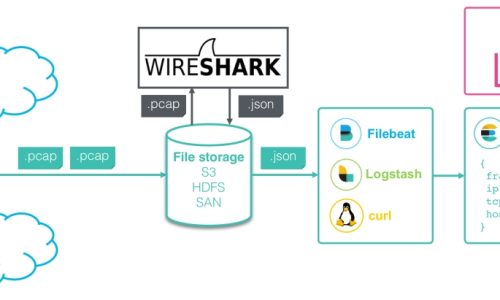
Wireshark Network Analysis
Sass is completely compatible with all versions of CSS. We take this compatibility seriously, so that you can seamlessly use any available CSS libraries.
Vulnerability Assessment
Less is a CSS pre-processor, meaning that it extends the CSS language, adding features that allow variables, mixins, functions and many other techniques that…








1 Comment
It抯 really a nice and helpful piece of information. I抦 glad that you shared this useful information with us. Please keep us up to date like this. Thanks for sharing.